PC settings, updates, maintenance, settings
Sections of the site
- Editor's Choice:
- Setting up shared folder access over a network in Windows
- Rambler - a search engine that no longer exists (from its heyday to its decline)
- Peer-to-Peer technologies - from Cinderella to princesses What is the peer to peer protocol
- Smartphone Samsung Galaxy A5 (2017) Black (SM-A520F) - Reviews
- Test review of LG G4s: a simplified flagship Specifications of LG G4s
- How to unlink a Xiaomi smartphone from a Mi account Unlink a device from a xiaomi account
- Determining the laptop model - simple ways
- Lenovo Vibe Z2 - Specifications
- Recovery: what is it and how to use it?
Advertising
| Service |
|
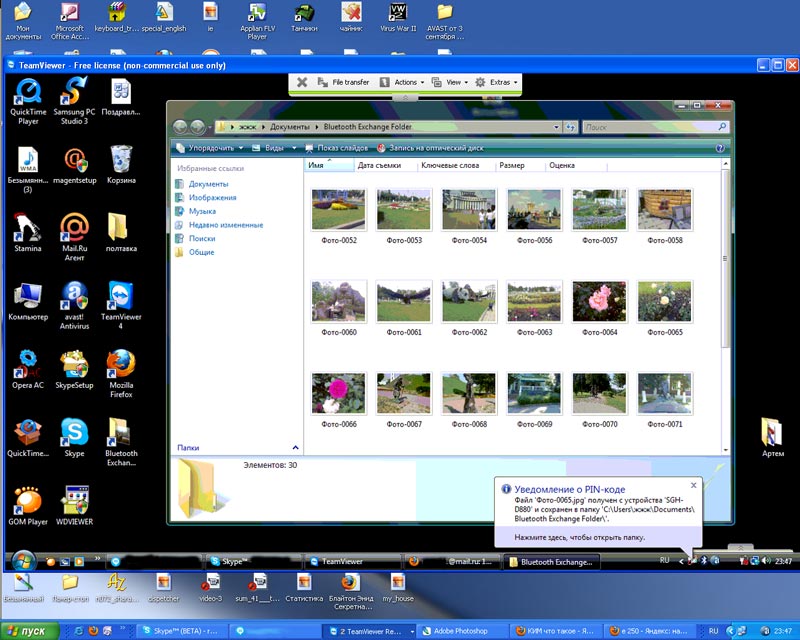
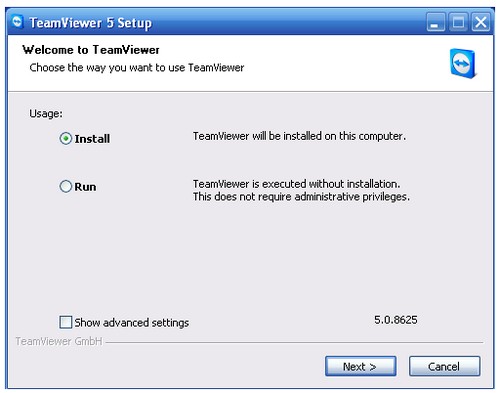
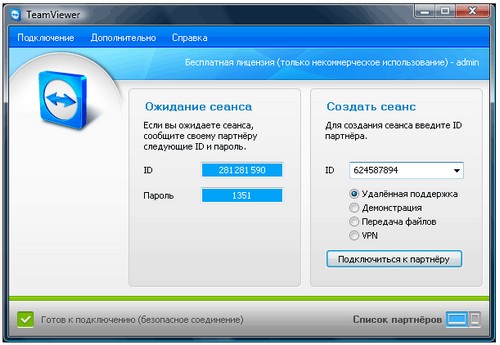
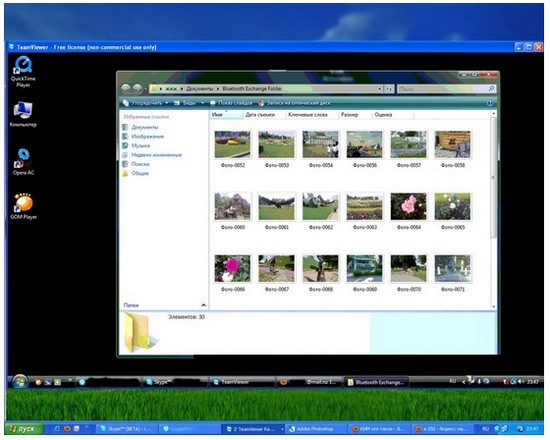
Is it possible to connect to someone else's computer? Network access to someone else’s screen: connect remotely to a computer via the Internet So, we received a new question: “” There are two options for connecting to a computer via the Internet: authorized and unauthorized. Those. in the first case, you gain access to someone else's computer with the permission of its owner, and in the second, you hack the computer's security using appropriate malicious software. In addition, there is the possibility remote control through applications for mobile devices. This allows you to test software without complex risk and make complex settings for the sample. The software is also suitable for data recovery. If there is an error in the system, you can reboot the device to the point where it is still faulty. If you are interested in this tool, you can find more information here. Tools without intermediary services. You can see the screen resolution in real time and control another computer using your mouse and keyboard. Files can be shared and a chat function is available. The exchange of information is encrypted. For more information, please click here. So let’s consider this case: somewhere far from you (or maybe not very far but you’re too lazy to go) your friend, brother, matchmaker, etc. lives. and so on. who is poorly versed in computer technology, but he cannot do this on his own. Your friend has Skype installed, but you can’t really explain anything to him in words. There is only one thing left: to do everything yourself, but in such a way as not to leave your familiar workplace. Mouse or keyboard inputs are immediately transmitted as if you were directly in front of it. You can interact with these computers over the Internet as well as through local networks. They are especially suitable for large and distributed networks. If you are interested Additional Information, Click here. However, when the connection is made in local network, speed is acceptable. Then you can use this computer to normal operation, opening programs and editing documents using the mouse and keyboard. Submitted free programs best suited for beginners. However, if you are looking for reliable and powerful software for remote control your business, consider premium software. Step 1. So, first of all, both you and your friend must install the appropriate software. Naturally, it is desirable that the installation does not cause any difficulties. For this reason, I strongly recommend using the TeamViewer program. The program is free under the condition of non-commercial use, i.e. in your home you can use it completely free of charge and on completely legal grounds. Free remote maintenance software at a glance. For professional use of remote service software in your company to support clients and employees, it is worth investing in paid tools. They offer a wider range of features to suit your needs. In addition, they are generally much easier to process. Features provided include replaceable screen transmission, remote diagnostics for hardware and software configurations based on system information, sharing files, multi-monitor support, annotation tools, and the supporter's ability to hold up to eight simultaneous sessions can be achieved. The software is especially suitable for companies that provide internal support from employees and external support clients. The remote control can also be done using mobile device applications. As you can see from the picture, you have two options: Install and Run. If you select the first option, TeamViewer will be installed on your computer. If you do not want to install the program, you can run it without installation by selecting the Run option (you must have administrator rights). Step 3. After you install and launch TeamViewer, the following window will appear: Various license models are offered. The price is 49 euros per month, billed monthly. This is a premium service with a subscription model. You have unlimited access to all programs; Emails you can read, edit documents and download files. Companies providing internal and external support are well aware of this service. It has the ability to be remotely controlled via mobile device applications. For advanced and professional users paid subscription may be useful. However, for most private users this tool became uninteresting after its disappearance free service. When problems are resolved, access to software and hardware inventory helps, as does monitoring services and displaying system configurations. Multiple receivers can be displayed on the operator's screen, so the service is also good for training. In order for you to connect to someone else’s computer, its owner must tell you (for example, using Skype) his ID and Password (or you must provide your data so that you can connect to your computer). The received data must be entered in the field on the right; you must enter the ID received from the partner and click the “Connect to partner” button. Next, you will be asked to enter the password received from your partner and after a couple of moments you will be able to see his desktop on your computer screen. This is a complete product and there are no ongoing subscription fees. For example, a technician may access multiple computers to perform updates, or multiple technicians may access the same computer to resolve a problem together. Remote access via the Internet is possible, but difficult. A special feature is the ability to make phone calls on remote session with one opposite video. In addition, there is also a separate script system, for example for process and software automation, as well as the possibility of remote control via mobile device applications. If you are just experimenting, you can connect to a test computer by typing 12345 as the ID number. Step 4. Well, everything is already very clear here. You grab a mouse and start operating on someone else’s computer. For example, I had to install antiviruses and organize accumulated photographs, which is depicted in the figure. Various licensing models are available. The special thing is that you have global network servers, so you don't need to use, for example, insecure cloud services for important business secrets. Unlike most other remote desktops, this tool is very fast in terms of image transfer, so it works smoothly - unlike image transfer from many other providers. The speed is based on the latest techniques, which also improves image quality. All the features are available with a few clicks as the user interface is uncomplicated which in turn means easy operation. The same method used in online banking means that both parties have encrypted authentication, resulting in a high level of security.
As you know, TeamViewer program designed to legally connect to someone else's computer via the Internet. To make an unauthorized connection, a Trojan is installed on the victim’s computer, which allows you to secretly control someone else’s computer. As you understand, all this is illegal and for this reason detailed information You won't find any information on this issue here. Usage For sporadic private use this service is free, for business use there are different tariffs from which you can choose the right one. Extensive reports on software and hardware and automated routine administrative tasks. Review of paid tools. Services such as those presented here often carry the risk of abuse and malware, such as Trojan horses: access and control capabilities lure hackers. Therefore, most of these tools provide encryption for sending information. If you have any questions about installing and working with the TeamVeawer program, then leave a message and we will try to answer. Hello dear guests and readers of the blog site. In this article I will tell you how to get remote access to another computer or how to control someone else's computer via the Internet. There are two ways to control someone else's computer via the Internet, namely legal and illegal. A legal way is when you gain access to someone else's computer via the Internet, with the permission of its owner. Well, the second method is when you gain access to someone else’s computer without the permission of the computer owner, simply by hacking using . Remote maintenance software or remote access also provides access to remote computers through the Internet. Various instruments have different functions depending on intended use. For private users, free programs are sufficient in most cases; companies and companies specializing in customer or employee support should consider purchasing a paid product. Features that provide access to other machines always pose a security risk, but most tools of this type take them into account and take steps to prevent them. How to remotely access another computerWe will focus on the legal way to gain remote access to another computer through Internet, that is, with the mutual consent of his owner and with his help. To gain access to someone else's computer, we will use a very simple and easy program, entitled "TeamViewer". This program is completely free, subject to non-commercial use, that is, legal grounds for home use. We also provide our partners with a remote service system to optimize customer service. Remote access must be allowed by the client without any major issues and at the same time counteract security risks. If you have further questions on this matter, please contact us at any time so that we can clarify this in a private discussion.
1 – Firstly, in order to receive access to another computer, you and the owner of the second computer must download this program to your computer. The best way to do this is from the official website by going to:
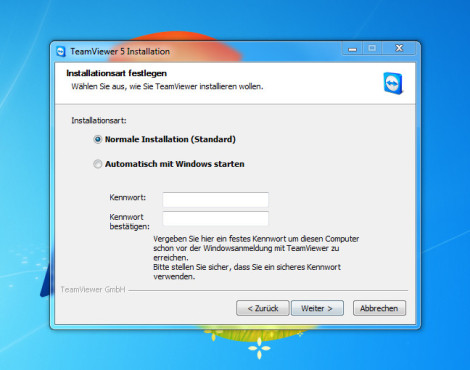
2- After you have downloaded the program, run it. A window will open with two options “Install” and “Run”. When you select “Install”, the program will be installed on your computer, and when you select “Run”, the program will start without installation.
3 – After you have installed the program, a window will appear with the words “ID” and “Password”. Now, in order for you to have access to someone else’s computer, its owner must tell you his ID and password, which will appear after installing the program. After you receive the ID address and password, you need to enter them into the program, first enter the ID, press "Connect to partner". And after that the program will ask for a password, enter the password. Well, that’s all, in a few seconds your partner’s desktop will appear on your screen. Help with just a few clicks. If the start of the session was successful, you will see your virtual partner's user interface. Therefore, allow remote service only to people you trust. In an emergency, click on the red cross on top panel control allows you to cancel the session. Nowadays, computers act as safes where we store all kinds of valuable information, from online service passwords to our bank account details. However, computers are not particularly secure. As our online addiction grows, so does the activity of computer thieves. October saw the worst cyberattack in the United States in 10 years, affecting billions of users.
Once you and your partner decide to use this program, it will be nice to know - from prying eyes. |
| Read: |
|---|
Popular:
New
- Rambler - a search engine that no longer exists (from its heyday to its decline)
- Peer-to-Peer technologies - from Cinderella to princesses What is the peer to peer protocol
- Smartphone Samsung Galaxy A5 (2017) Black (SM-A520F) - Reviews
- Test review of LG G4s: a simplified flagship Specifications of LG G4s
- How to unlink a Xiaomi smartphone from a Mi account Unlink a device from a xiaomi account
- Determining the laptop model - simple ways
- Lenovo Vibe Z2 - Specifications
- Recovery: what is it and how to use it?
- Factory reset Sony Xperia XA Dual
- How to install the DHT Personalization app